Gavin Holt, who I was fortunate enough to be mentor to for last years BSides London Rookie track, invited me to submit a talk for Securi-Tay3, the third annual security conference hosted by the University of Abertay and run by the Abertay Hackers Society. He is the Vice President of that society and responsible for drumming up trade for the conference. Securi-Tay has a reputation for being Scotland’s biggest security conference, and this year attracted something like 170 people putting it well on a par with many ‘professional’ conferences.
Gavin Holt, who I was fortunate enough to be mentor to for last years BSides London Rookie track, invited me to submit a talk for Securi-Tay3, the third annual security conference hosted by the University of Abertay and run by the Abertay Hackers Society. He is the Vice President of that society and responsible for drumming up trade for the conference. Securi-Tay has a reputation for being Scotland’s biggest security conference, and this year attracted something like 170 people putting it well on a par with many ‘professional’ conferences.
I duly did as I was told and submitted into the CFP.
The day was great; the conference was well managed and run, there were always plenty of volunteers in distinctive blue (and not black for once!) T-shirts who were friendly and willing to help. Vitally there was always a cup of tea available in the reception area, throughout the day, something so many conferences miss when you are working the hallway track rather than the advertised tracks. This is one Englishman who has traditional standards…
As expected there was a very strong technical slant to the presentations (many of them given by people called Rory it seems as well) and some of them were beyond me. In fact I tweeted the following day saying that the one downside to the conference was that I often felt like the dumbest person in the room.
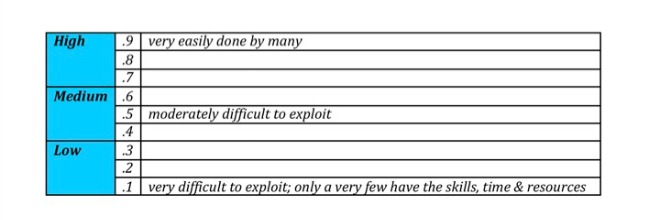
I was able to present on “Throwing Shapes for Better Security Risk Management”, a wholly revamped version of a talk I did at the IT Security Forum late last year. When I first gave it I had some great feedback from Jitender Arora which I tried to address, as well as the formal feedback from the session (basically “good content but not what was promised”). Securi-Tay kindly recorded the talk which I will post shortly, although with the microphone cutting out there is only so much you can hear. Feedback afterwards was very positive, and I had some great conversations with people not just about risk management but presentation style generally.
Two other presentation also stood out for me; Ritesh Sinha and Paco Hope‘s “The Colour of Your Box: The Art and Science of Security Testing” and Rory McCune’s “Crossing the Mountains of Madness – How to Avoid Being a Security Cultist”. These will also be available at the Securi-Tay YouTube channel shortly.
This was a great conference, attended by people who truly wanted to learn and engage rather than just get out of the office for the day, and who are actively pursuing a career in the infosec industry. What did surprise me though was the number of people from the day who wanted to get more involved with risk management as a career option rather than the more technically focussed, ethical hacking option which at first glance would appear to be the defacto choice. The honesty and passion of all of the students there was very refreshing, and I thoroughly enjoyed chatting to everyone at the after party, all the way through the inevitable kebab on the way back to the hotel.
A big thank you to Gill Chalmers, Gavin Holt and all of the members of the Abertay Ethical Hacking Society for running an educational and excellent day.