I decided to write a review of a paper submitted to wired.com on the subject of “An Approach to Risk Decision Making” by Curt Dalton. I must however declare an interest in this, in that I happen to report to Curt in my day job (he is global CISO), and that he was kind enough to share drafts with me as he wrote it for feedback. This will of course therefore be a somewhat biased review, although not too much, but I do hope if nothing else it generates conversation around topics and approaches like this. I have a huge respect for Curt, have learnt much from him over the last few years and hope to get a good score in the next performance review!
In essence, this model is designed to help an orgnaisation decide if it is financially viable to invest in security technology/controls/procedures in order to address a given risk. It is not designed to be used across an organisations risk management porogramme, but rather with those handful of risks that can’t be addressed in day to day operations and have to be escalated to senior management to be effectively resolved. With limited budget and access to that senior leadership, this approach provides support and guidance on what to ‘fix’ and what not to fix.
This scope is a key element of the model; it uses very traditional approaches to monetizing risk versus the more in vogue approach I have reviewed elsewhere in this blog. To that end it uses assigned numerical values to elements of its calculations; this is of course where ‘errors’ may creep in, but in theory an experienced risk manager familiar with their environment should be able to assess this reasonably well.
In summary, the model is as follows:
Figure 2 in the model requires an analysis of controls required to address a risk.
This does of course beg the question, how do you know you have all of the controls required and how do you know you have selected the correct numerical value? Again, the pragmatist in me suggests this is entirely possible with someone who is familiar with the environment and the organisation, but this may of course be more difficult in other situations.
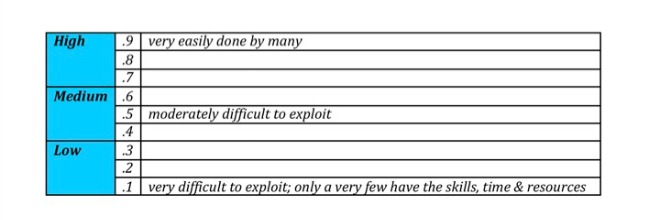
Figure 3 does a similar thing with a similar level of granularity, i.e. defining in nine increments the ease of exploitation of a given risk; where I think there is potentially something missing is that this value applies to ALL of the risks listed in figure 2 rather than individually.
Obviously this would massively increase the complexity of the solution but this is a deliberate approach to ensure simplicity across the model.
These two numbers are then combined with a simple calculation of impact to etsablish a level of monetized risk. Finally, the 80/20 rule (or Pareto’s Principal) is used as a rule of thunmb to define the actual budget that should be spent to mitigate a risk. In the example given therefore a monetized risk of roughly $1.5m USD should be mitigated by spending up to $380k USD and no more. The Pareto Principal can of course be adjusted accoring to your organisations risk appetite, that is, the more risk averse the organisation the more the rule would move from 80/20 to 70/30 or 60/40 etc..
There are a lot of assumptions used in this model, not least the numerical values that may seem to be arbitrarily assigned. However, I believe this can be forgiven for the very simple reason that this is a pragmatic, transparent and easily understood approach; it can be easily transferred into an Excel spreadsheet meaning that some simple modelling can be carried out. I have said before that until the newer approach to risk management has a more easily understood and implentable approach it will not be adopted. This model does.
The other part to this model that I like is that it is not designed to be a cure all, but rather a tool to help organisations decide where to spend money. If the approach is understood then an informed decision can be made within the constraints of that model (or indeed any other model). I believe it is influenced by the ISO27005 approach to risk management which means many risk management folks will be able to grasp and adopt it more easily.
Overall, this is a model that can be adopted quickly and easily by many organisations, and implemented successfully, as long as its basis in assigning numerical values is understood, and calculations are carried out by those in a position to understand their risk profile well. I would strongly recommend you tai a look at the model yourself over at Wired Innovation Insights.
Pros – easily understand, pragmatic, focussed on one business issue, easily implemented.
Cons – relies on assigning ‘arbitrary’ numerical values, doesn’t address granularity of risk and ease of exploiutation.