 It was ten to six in the morning, and I was on the station platform waiting for my train to arrive to take me to London. As I walked past two people who were talking, one of them was earnestly telling the other about problems in his office that were caused by “them”:
It was ten to six in the morning, and I was on the station platform waiting for my train to arrive to take me to London. As I walked past two people who were talking, one of them was earnestly telling the other about problems in his office that were caused by “them”:
they’ve changed the heating in the office to make it more consistent apparently but what they don’t realise is that it is sending us all to sleep. They just don’t get it, they’re idiots, and it’s a waste of money
It seems the faceless bureaucrats and management just don’t get it at this gentleman’s place of work and are doing everything they can to hinder the company’s ability to work effectively! But scratch a bit deeper and you may see a slightly different story of trying to deal with complaints from parts of the building that are too cold, using antiquated heating systems that don’t balance heat well the further from the heat source they are, or even just trying to make everyone feel more comfortable in the cold winter months.
The unfortunate impact of their actions though is that productivity has dropped in some areas, and the impression of the team and people behind it has dramatically reduced.
I have regularly stressed the importance of information security ultimately contributing to the success of the business, allowing it to sell more beer if you will, but that is only possible if you understand the business, collaborate with the people on the ground, and align your efforts to their goals. By treating risks in isolated parts of the business without looking at the wider impacts you run the risk of overheating other parts of the business. What initial makes sense in one place does not make sense in another, and the quick win you thought you had really turns out to require a far more nuanced approach.
If what you are doing is simply unavoidable and impacts to the other parts of the business will be felt, then collaboration and communication is vital. Explaining the complaints, challenges, risks etc. and allowing them to voice their feedback is important to ensure people remain bought into your plans. Who knows, you may actually get some better ideas from them that you hadn’t even considered. This approach requires nerves of steel and the skin of a rhino though, as many will see the opportunity to take a swipe at you, but seeing the process through is far more effective in the long term.
Asking for feedback afterwards, chatting to individuals and leadership about what they think about what you have done, and putting that feedback to work to improve your next iteration of the programme all help bring people on side and improve the effectiveness of your information security stance.
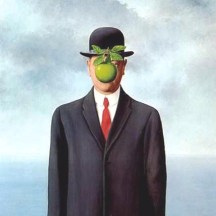
Once you are seen to be working in the long term interests of the company and the people who work there, decisions you take and implement will be seen in that wider context, and not just as the actions of someone just “doing their job” and being one of… them.








